Office 365 Advanced Threat Protection, formerly known as Microsoft Defender for Office 365, provides powerful protection against viruses and other threats.
You can protect your Exchange Online, Teams, SharePoint Online, and OneDrive against malicious content by using tools such as Safe-Links and Safe-Attachments.
In Exchange Online, Advanced Anti-Phishing Policies are available to further protect against phishing. Defender for Office 365 Plan 1 provides all of these solutions as an add-on.
In Plan 2, you will be able to discover and report on potential issues in your environment by leveraging tools such as Threat Tracker and Explorer. In addition, you can use Attack Simulations to create Malware / Phishing campaigns that keep users alert.
Office 365 Defender: Getting Started Guide
Many configuration options and thresholds are available in Defender for Office 365 that gets customized according to policy and requirements. The sea of checkboxes and buttons can be overwhelming when you’re just getting started.
Thanks to Microsoft’s recommendations for EOP and Defender for Office 365, we’ve been given some great information about this. For your initial setup, please use the information provided here as a guide so that you can align with Microsoft’s recommendations.
The document will need to be read through thoroughly and the configuration updated accordingly to the guidelines. Run the Office 365 Advanced Threat Protection Recommended Configuration Analyzer (ORCA) to determine how Defender for Office 365 is configured.
There are so many configurable features with Defender for Office 365 with so many configurable features. The following main categories will hopefully make things more transparent:
- Anti-Phishing
- Anti-Spam
- Anti-Malware
- Safe Links and Safe Attachments
In context, we assume that Configuration Analyzer gets used to apply – or review – the standard Microsoft recommendations throughout the organisation.
Phishing Policy: Protect domains and users with Impersonation Protection
Defenders for Office 365 can’t know which users or domains are sensitive to your organization. It is essential to consider more advanced attacks, like whaling, when defining anti-phishing policies.
It is a practice in which an attacker performs a highly targeted phishing attempt under the guise of a high-ranking official at an organization, such as the CEO or CFO.
Due to its importance or urgency, the phishing attempt seems like an important message, making the recipient more likely to believe it. Commonly, recipients act quickly before considering the validity of e-mails claiming to be from an organization’s CFO and requesting urgent payment details.
Users and Domains to Protect settings enable you to specify internal and external users and domains to protect against spoofing.
In the policy assignment process, the policy assignment is done by choosing the policy owner, a decision that the policy owner must make.
It is a powerful way of protecting essential users such as the CEO of a partner organisation if used for every contact, internal and external. With Configuration Analyser, you will be able to secure the domains you accept in your organisation. Still, any critical domains of your partners or suppliers need to be protected as well.
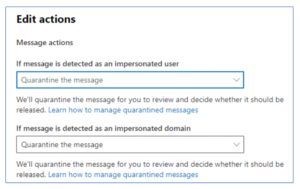
In the actions section of this dialogue, you can choose the action to be taken once the Impersonation Protection setting has been enabled for these users and domains.
Impersonation protection: Enable Mailbox Intelligence Anti-Phishing Policy
By leveraging machine learning, Defender for Office 365 creates each user’s “sender map” based on their communication patterns. A spoofing attempt gets effectively undermined by using the data gathered to inform the Defender’s decision-making. Impersonation protection is not available with Mailbox Intelligence as part of the baseline.
Adding Impersonation Protection to Mailbox Intelligence can assist in improving the results of the Mailbox Intelligence capabilities.
First Contact Safety Tips – Enable anti-phishing policy
It appears that Configuration Analyzer has not captured First Contact Safety Tips, a relatively new addition to Defender for Office 365.

Credit: practical 365 (figure 3)
Using this setting, the user receives a tip on unidentified mail when receiving an e-mail from an unknown address.
Users can get notified of unknown addresses when they receive mail from them, which is particularly useful to remain alert:
By the time this setting is standard, it is worth manually enabling users to detect potential spam and phishing attempts from unknown addresses. In the Anti-Phishing Policy, you can find this setting under ‘Actions’.
Defining a Phishing Threshold: An Anti-Phishing Policy
The probability of a message being a genuine Phishing attempt is determined by Defender’s confidence in such an attempt. Depending on the confidence level, it could be ‘low’, ‘medium’, ‘high’ or ‘very high’. The story of confidence is then applied to messages.
The Phishing Threshold setting for the baseline is 2 (aggressive). If either a ‘high’ or a ‘very high’ is marked, that means that a spam filter will consider it very high confidence and take the appropriate action, while ‘low’ and ‘medium’ can take a different path.
Credit: practical 365 (figure 1)
The value set for this threshold is highly dependent on the organisation, industry, and associated risk, as with most of the entries in the Defender suite. However, this value needs to be monitored and adjusted if necessary. We do not recommend changing it on day one.
Using this threshold to toughen security can be helpful if your protections are still getting compromised even after you have active preventions in place. Alternatively, if your organisation is receiving too many false positives, it may be worthwhile to consider lowering your threshold. It should also be considered what the Anti-spam Phishing and High Confidence Phishing settings described in the Anti-Spam policy section assign as actions.
Mail-stopping software
Spam Properties (ASF) are configured as part of the Anti-Spam policy. The Configuration Analyzer does not configure this. We are deprecating ASF settings as part of the Anti-Spam policy, and these protections will get incorporated into other platforms components shortly. In the future, new configurations should avoid the use of ASF settings.
An anti-malware program
Files and emails contain malicious content that would affect Anti-Malware Policies. Generally, there is limited configuration within Anti-malware settings, but you may want to review a few options not covered by baselines.
Standard Attachments Filter: Protection against malware
Baseline data indicate that the typical attachment filter blocks the following file types (Figure 4), covering the most commonly blocked file types. The standard attachments filter is designed to block most extensions unless there is a legitimate need to allow them.
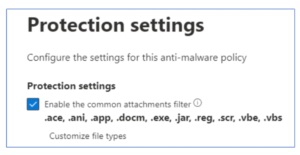
Credit: practical 365 (figure 4)
It strongly recommends using a ‘whitelist’ approach to select what types you don’t want to block, as it covers many undesirable file types. You might be able to review the Microsoft list to find out what styles you don’t want to stop.
Configure notifications for the anti-malware policy
In the Anti-Malware policy, several types of notifications get configured to notify various parties. You could potentially share sensitive configuration information with an external sender if you inform them after a block.
Credit: practical 365
Although notifying internal recipients when items are quarantined is good practice, in our opinion is that the most important configuration is to alert administrators when malware is detected.
It will be possible for administrators to track when malware is blocked by forwarding reports from the options for NOTIFY AN ADMIN ABOUTUNDERED MAIL from internal senders and FROM EXTERNAL SENDERS to a monitored security mailbox:
Linking to and attaching to safe sites
If you haven’t created a Safe Links or Safe Attachments policy in your tenancy before configuring Defender for Office 365 using Configuration Analyzer, Safe Attachments aren’t shown. If it is not in place, this may give the impression that everything is just fine. Once it is created, the first policies become part of the configuration. Again, once the baselines are established in Configuration Analyzer, other settings get checked after setting up the baselines.
Set SharePoint, OneDrive, and Teams Safe Attachments to True
It’s possible to enable the Safe Attachments to feature for SharePoint, OneDrive and Teams from the Safe Attachments ‘Global Settings’. If the exchange authentication is being used for Teams or SharePoint, this setting gets considered to extend the exchange authentication to other parts of the platform.
Global setting: Enable Safe Attachments for Office clients
When Safe Documents is enabled for Office Clients, Microsoft Defender for Endpoint is invoked before opening any files. Microsoft 365 E5 and E5 Security licenses must access Safe Documents (mainly because of the integration with the Defender for Endpoint service).
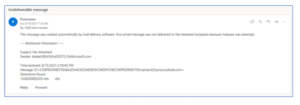
The feature will prevent users from editing protected-view files until they have been scanned. Users will not see the ‘Enable Editing’ option if the file is detected as malicious and will see this message instead:

Credit: practical 365
Safe Documents has the option to allow people to open protected views even if the file is malicious, but we do not recommend enabling this outside of testing.
Implementing Safe Attachments Policy for non-Hybrid Environments
It is possible to configure Safe Attachments to prevent emails from being sent with malicious attachments to mailboxes that are not present in Exchange Online or replace the malicious attachment with a generic one while allowing the regular email to flow.
The Defender can investigate attachments with either of these options.
The Dynamic Delivery feature gets enabled if Exchange Online hosts all mailboxes. The attachments get stripped from email messages upon delivery. Following delivery, the Defender scans the attachments and redelivers them to the email. End users’ productivity is minimized as a result of this scanning process.
Defender for Office 365 baselines are a great way to get it put in place quickly in your environment, but they do not complete the installation for you.
You should still review and tweak a few items to suit your organization. These items represent a subset of the many available to you, but in conjunction with the baselines, will help you develop your Defender implementation even further.