The digital age is changing corporate operations on all levels, bringing both opportunities and problems. So, organisations in Australia use cloud computing, machine learning, and mobile devices to improve productivity and cut expenses. However, these same technologies expose corporations to more sophisticated cyberattacks.
To effectively manage cybersecurity issues, it is critical to start with best-practice procedures. The Australian Signals Directorate (ASD) and the Australian Cybersecurity Centre (ACSC) have created the Essential 8 Model, a government-led cybersecurity project. Businesses can immediately strengthen their cyber security posture by adopting these general suggestions, which do not require large investments or study.
In this comprehensive guide, we will take a close look at each phase of the model and help you understand the ASD Essential Eight Maturity Model and how you can implement it in your business or startup to progress to the next level.
What is the Essential 8 Maturity Model?
The Essential Eight Maturity Model is a framework developed and maintained by the Australian Cyber Security Centre (ACSC) for analysing and enhancing an organisation’s cybersecurity posture.
It was first released in June 2017 and has since been continuously updated to help implement the Essential Eight. This strategy is based on the ACSC’s extensive experience producing cyber threat intelligence reports, detecting cyber security events, conducting penetration testing, and helping organisations adopt security measures.
It focuses on eight major mitigation strategies: application whitelisting, application patching, operating system patching, administrative privilege control, remote access technology restriction, multi-factor authentication, daily backups and configuration management.
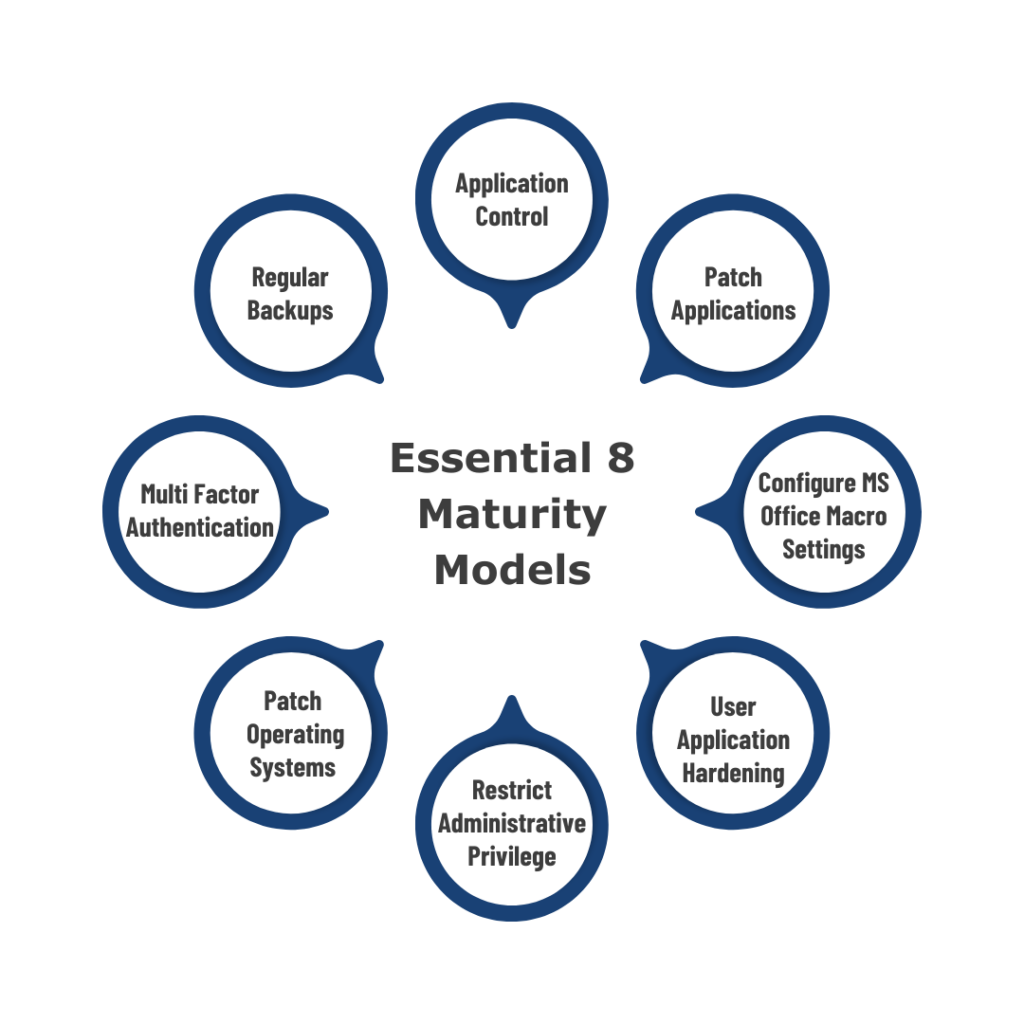
List of Essential Eight Maturity Models
Following are the lists of Essential Eight maturity models maintained by the Australian Signals Directorate (ASD) and the Australian Cybersecurity Centre (ACSC).
- First Model: Application Control
- Second Model: Patch Applications
- Third Model: Configure Microsoft Office macro settings
- Fourth Model: User application hardening
- Fifth Model: Restrict administrative privileges
- Sixth Model: Patch operating systems
- Seventh Model: Multi-factor authentication
- Eighth Model: Regular backups
The latest updates of the ASD Essential Eight model, made in November 2023, focus on changes in the implementation and risk assessment methodology. These modifications aim to address the evolving cyber threat landscape and enhance the effectiveness of the model in protecting organisations from potential risks. Now, let’s discuss these maturity models in detail.
Application Control
Application control is used to allow or deny the execution of programs on your network. Only permitted programs can execute in your environment, and other applications cannot access your data. It was developed to block the execution of unauthorised/malicious programs such as .exe, DLL, scripts (e.g., Windows Script Host, PowerShell, and HTA), and installers.
According to the latest update, it’s important to conduct annual evaluations of application control rule sets and follow Microsoft’s recommended application block list at Maturity Level Two.
Patch Applications
Unpatched applications are popular targets for attackers. Patching apps decreases vulnerabilities in operating systems, including Flash, Microsoft Office, web browsers, Java, and PDF software. Patch mitigate computers with ‘high risk’ vulnerabilities within 48 hours, and use the latest version of the applications to prevent attackers from exploiting them.
However, the latest update gives patching scenarios more importance, particularly for serious vulnerabilities. Organisations must update, patch, or mitigate such vulnerabilities within 48 hours. Applications that interact with untrusted content must be patched within two weeks.
Configure Microsoft Office macro settings
Microsoft Office macros can automate processes throughout an Office productivity suite but can also be exploited maliciously. The Essential 8 guidelines include deactivating Microsoft Office macros for users with no documented business necessity at a higher maturity level. You should modify Microsoft Office macro settings to prevent macros from being downloaded from the Internet and only allow verified macros that are either in ‘trusted places’ with limited write access or were digitally signed with a trustworthy certificate.
According to new updates, the Macro execution event will be removed due to limited benefits and implementation challenges. The Maturity level three requires V3 digital signatures.
User application hardening
Application hardening aims to reduce the possibility that end-user applications include dangerous code. The Essential 8 user application hardening technique suggests configuring web browsers to prevent Flash (preferably uninstalled), advertising, and Java on the web. Disabling unnecessary functionality in Microsoft Office (e.g., OLE), web browsers and PDF software. Auto-discovery for databases and middleware is a crucial requirement for hardening, and every solution should contain it.
According to the latest update, organisations must disable or delete Internet Explorer 11 following the discontinuation of support for it. The emphasis is on applying ASD and vendor hardening guidelines while prioritising the most stringent criteria. This includes PowerShell logging and command-line process creation events at Maturity Levels Two and Three.
Restrict administrative privileges
Restricting administrator rights is an excellent way to prevent accidental or deliberate system hacks and data breaches. It makes generic advice based on user tasks for managing privileged access to systems and applications. Also, periodically evaluate the necessity for privileges. Limit the use of privileged accounts for email and web browsing. Privileged access should be validated, restricted to certain tasks, and automatically disabled after a set period of inactivity.
According to the latest update, Governance procedures for privileged access, such as data repositories, must improve. Privileged accounts that use the internet must be expressly identified and limited. The requirements for protected admin workstations, break glass accounts, and infrastructure hardening are introduced.
Patch operating systems
Patch management prioritises timely updates, patches, and vulnerability remediation for OS of workstations and internet-based services. If a vulnerability exists, it should be addressed within 48 hours. You should patch or mitigate ‘high risk’ computer vulnerabilities (including network devices) within 48 hours and utilise the most recent operating system version. Unsupported versions are vulnerable to attacks therefore avoid using them.
However, the latest update gives patching scenarios more importance, particularly for serious vulnerabilities. Organisations must update, patch, or mitigate such vulnerabilities within 48 hours. Operating systems that interact with untrusted content must be patched within two weeks.
Multi-factor authentication
For Internet-based services, Essential 8 strategies urge that employees adopt multi-factor authentication. In addition, third-party Internet-based services for sensitive and non-sensitive company data and all users performing privileged actions or accessing a critical (sensitive/high-availability) data area to avoid impersonation, including VPNs, RDP, SSH, and other remote access. Multi-factor authentication has become a widely accepted standard for improving access to systems and services that rely on a single password, code sent to a mobile number, or biometrics identification.
The MFA has tightened its rules in the latest update of the Essential Eight models. The updated standard at Maturity Level One adds “something users have” in addition to “something users know.” Sensitive data ports must now use multi-factor authentication (MFA), focusing on phishing-resistant MFA. Maturity Level 2 requires organisations to impose multi-factor authentication (MFA) for employees logging onto business systems.
Regular backups
The eighth maturity model refers to a collection of backup and data protection rules. Daily backups of vital, new, or modified data, software, and configuration settings should be made and stored separately for at least three months. Furthermore, the recovery of systems, software, and essential data from backups should be validated in a coordinated manner during disaster recovery. This improves business continuity and facilitates faster recovery from a successful attack.
There are no significant changes in the latest update. However, businesses are recommended to prioritise backups based on the business criticality of the data. This affects Maturity Levels One to Three.
How do you implement the Essential Eight Maturity Model?
To apply the Essential 8 maturity model, companies must first analyse their present degree of security using the maturity model’s framework. They can then prioritise and implement mitigation techniques while continuously monitoring and improving their cybersecurity posture.
Essential eight comprises eight different security controls, when implemented, will work together to protect against various cyber threats. When using the Australian Signals Directorate Essential 8 maturity model, set a target maturity level and prepare to attain it before progressing to the highest maturity levels. Also, aim for the same maturity level across all eight techniques to offer complete protection.
To safeguard your company, use a risk-based approach to adopt the Essential Eight security controls. Implement compensating security controls to decrease the number and scope of exceptions. If you do have exceptions, make sure to document them and obtain approval through the proper process.
As a result, the necessity for exceptions and their related compensating security controls should be maintained and assessed regularly. It is important to note that the appropriate usage of exceptions should not prevent an organisation from being assessed as meeting the standards for a given maturity level.
What are the four maturity levels of the Essential Eight Maturity Models?
Organisations can utilise four maturity levels to guide the implementation of the eight essential security measures. The initial level, i.e., maturity level zero, represents the starting point. The subsequent levels (one through three) handle and mitigate more advanced adversarial tradecraft.
Depending on the adversary’s overall capacity, they may demonstrate varying levels of tradecraft for operations against other targets. For example, an adversary with advanced tradecraft may utilise it against one target while employing simple tradecraft against another.
As a result, organisations should consider what level of tradecraft and targeting rather than the adversaries they wish to mitigate.
Maturity level zero
This maturity level is appropriate for adversaries seeking to have access and control over systems using publicly available means. For example, an adversary could exploit a known security vulnerability in an unpatched internet-facing service or attempt to enter an internet-facing service using stolen, reused, brute-forced, or guessable credentials.
It is usual for adversaries to seek any victim rather than a specific one; they will exploit weaknesses in multiple targets rather than investing hard in acquiring access to a single target. Adversaries will utilise social engineering techniques to deceive users into compromising the security system, which will subsequently launch malicious programs. For example, this can be accomplished using Microsoft Office macros.
If an adversary gains access to an account with privileges, they may try to exploit it and potentially destroy data, including backups, based on their goals.
Maturity level one
This maturity level is for attackers who have gained high privileges on a network, most likely through exploiting flaws or using someone else’s credentials. At this point, adversaries use a variety of methods to avoid discovery and maintain access to systems, typically by utilising authorised administrator tools and changing system configurations.
Adversaries may also attempt to obtain credentials, increase privileges, and continue moving.
Maturity level two
This maturity level is intended for attackers who want to conceal their behaviour while maintaining access to a network, sometimes for extended durations. They utilise advanced strategies such as using genuine administrator tools in unexpected ways, as well as proprietary malware or methods that make it difficult to identify their presence on the network.
Adversaries at this stage may attempt to steal, influence, or disrupt network functioning.
Maturity level three
Adversaries at this level can use sophisticated techniques to conceal their presence on a network, such as supply chain compromises, hardware implants, and advanced custom malware that can evade detection. They can target specific individuals or organisations for espionage or sabotage.
Organisations after reaching the highest maturity level should have strong monitoring, detection, and response capabilities to reduce the highly sophisticated attacks they face.
What are the objectives of the Essential Eight?
The Australian Cyber Security Centre’s Strategies to Mitigate Cyber Security Incidents provides eight critical mitigation strategies that, while not guaranteed, will make it considerably more difficult for hackers. The Essential Eight are the fundamental defending strategies.
The ACSC Essential Eight implementation can save money, time, and effort compared to responding to a large-scale information security event.
The following lists are objectives of Essential Eight:
Prevent cyberattacks
The Essential 8 cyber security framework helps organisations prevent many types of cyberattacks by patching software and operating systems, limiting administrative rights, and implementing multi-factor authentication.
Identify threats
Implementing application control and daily backups enables businesses to detect potential risks in their systems and improve vulnerability management skills.
Cyber security Incident response
Using secure network device configurations and restricting the usage of outdated or insecure protocols allows businesses to respond to incidents more quickly and efficiently.
Recover from incidents
Essential 8 framework recommends implementing disposable data and backups to assist in recovery after a successful attack.
Data recovery and system availability
Assessing the implementation of Essential Eight measures also contributes to the system’s availability and data recovery following successful cyberattacks.
Why should you implement the Essential 8 framework?
Implementing Essential Eight can help you prevent, identify, and respond to various cyberattacks. It can also save you time, money, and effort in the long run by lowering the probability and severity of a successful attack. Adhering to the basic eight can indicate a commitment to cybersecurity while also meeting compliance requirements for businesses in Australia seeking to defend themselves from cyber threats.
What do the Essential Eight Maturity Models Mean for Organisations?
Essential Eight maturity models offer a framework for evaluating and improving cybersecurity practices. Organisations can strengthen their defences against common types of cyberattacks and demonstrate their commitment to cybersecurity by implementing these eight critical steps. The models also allow businesses to regularly examine and adjust security practices in response to emerging threats and technologies.
How to be compliant with the Essential Eight Maturity Models?
To comply with the major Eight maturity levels, companies should continuously assess and update their security processes to ensure that all eight key measures are implemented. This involves application control, patching and operating system updates, hardening user applications, limiting administrative privileges, implementing multi-factor authentication, and regularly backing up data.
Organisations can also use the Essential Eight Maturity Model self-assessment tools to determine their present level of compliance. These tools enable companies to monitor progress and identify areas for improvement to meet compliance requirements.
It is crucial to remember that compliance with the Essential Eight does not ensure total security against cyberattacks because threats are constantly developing. However, implementing these procedures can considerably improve an organisation’s defences against common types of attacks.
Conclusion
The Essential 8 Maturity Model is a great tool for organisations who want to better assess and reduce cybersecurity risks. Businesses may ensure that their systems meet industry standards and are secure against potential cyber threats by knowing each model component and tracking development over time.
Implementing the Essential 8 Maturity Model is an important step towards keeping your organisation ahead of cyber attackers.
How can NSW IT Support help to employ Essential Eight with its cybersecurity service?
As a full-service IT support company in Australia, NSW IT Support ensures that you receive the best IT services, followed by support, maintenance, and security. We are well aware that organisations are looking for the best online security solutions, ranging from Microsoft security solutions to MFA. As a result, we offer powerful cybersecurity services to ensure your online security.
We ensure that our IT consulting services include information about the eight important controls and assist businesses in developing an effective cybersecurity plan. Our cybersecurity services also focus on teaching people about what is going on in the cyber realm, what they can do to prevent it, and much more.
Contact us if you need full-fledged IT support. We will respond as quickly as possible.










